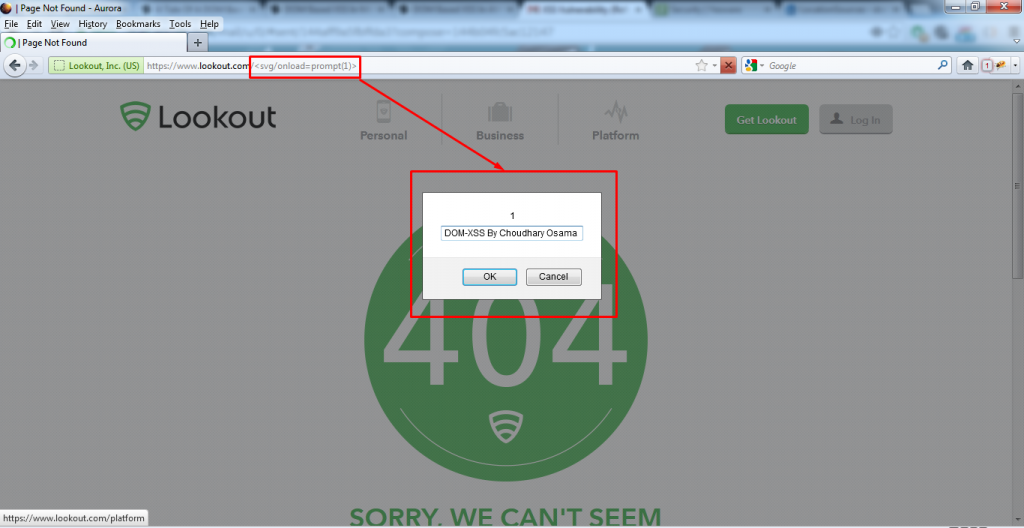
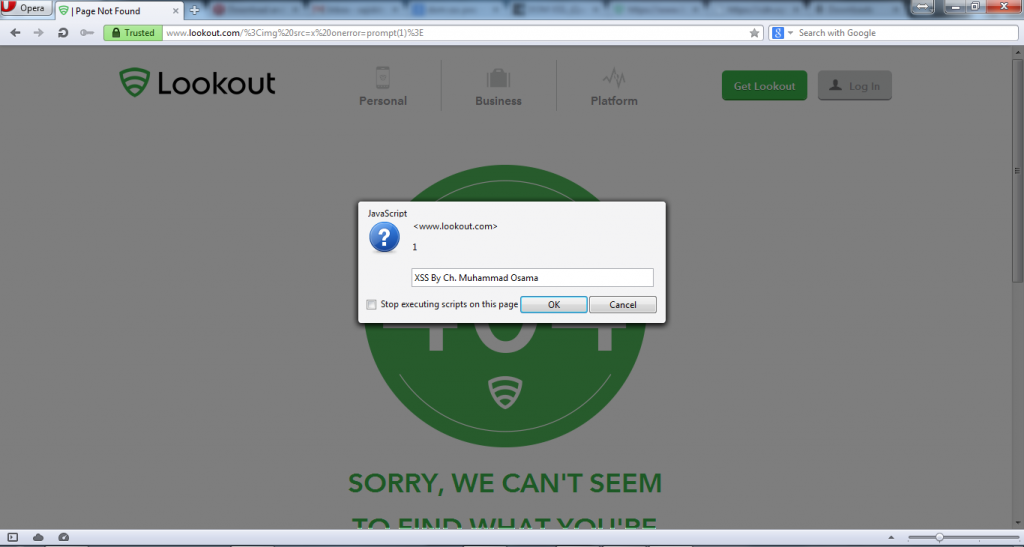
Ch. Muhammad Osama, an independent vulnerability researcher has discovered a DOM Cross-Site Scripting (XSS) vulnerability in Lookout website www.lookout.com, which can be exploited by an attacker to conduct XSS attacks.
DOM Cross-Site Scripting :-
DOM Based XSS (or as it is called in some texts, “type-0 XSS”) is an XSS attack wherein the attack payload is executed as a result of modifying the DOM “environment” in the victim’s browser used by the original client side script, so that the client side code runs in an “unexpected” manner. That is, the page itself (the HTTP response that is) does not change, but the client side code contained in the page executes differently due to the malicious modifications that have occurred in the DOM environment.
This is in contrast to other XSS attacks (stored or reflected), wherein the attack payload is placed in the response page (due to a server side flaw).
Proof of Concept :-
URL :- POC Link Here
Video Explanation :-
Conclusion :-
This vulnerability has been confirmed and patched by Lookout Security Team. I would like to thank them for their quick response to my report.
Status : Fixed!
Hall of Fame : Yes!
Bounty: No!


0 Comments